All source code for demo application and kubernetes manifests files can be found at demo
This is default and recommend usage for storing secret. The piggy is also support AWS System Manager (SSM) Parameter Store. To use SSM sees AWS SSM Parameter Store section below
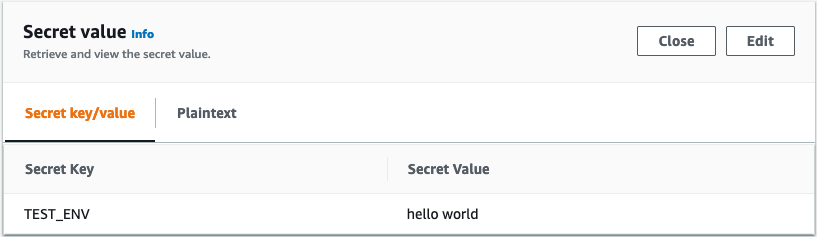
The demo here will retrieve the secret name TEST_ENV from AWS secret manager name demo/sample/test
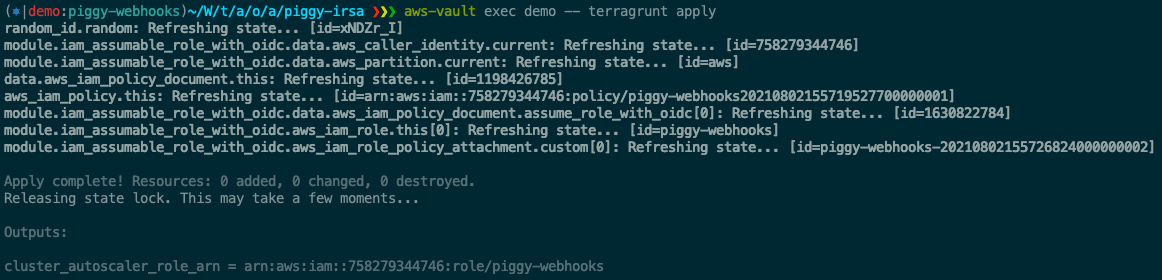
In this demo, I use terraform to create IRSA for piggy-webhooks namespace and service account.
The simplest IRSA Policy for Piggy webhooks
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "PiggySecretReadOnly",
"Action": [
"secretsmanager:DescribeSecret",
"secretsmanager:GetResourcePolicy",
"secretsmanager:GetSecretValue",
"secretsmanager:ListSecretVersionIds",
"secretsmanager:ListSecrets"
],
"Effect": "Allow",
"Resource": "*"
},
{
"Sid": "PiggyECRReadOnly",
"Action": [
"ecr:BatchCheckLayerAvailability",
"ecr:BatchGetImage",
"ecr:DescribeImages",
"ecr:GetAuthorizationToken",
"ecr:GetDownloadUrlForLayer"
],
"Effect": "Allow",
"Resource": "*"
}
]
}${piggy-role-arn} can be found from Role ARN which was created by terraform above
helm repo add piggysec https://piggysec.com
helm install piggy-webhooks piggysec/piggy-webhooks --set aws.roleArn=${piggy-role-arn}Check running piggy-webhooks pod
Now piggy-webhooks pod is ready, create a pod with annotations to piggy-webhooks service, secret name, and aws-region. You can see a yaml file at demo/proxy/pod.yaml
apiVersion: v1
kind: Pod
metadata:
name: demo
annotations:
piggysec.com/piggy-address: https://piggy-webhooks.piggy-webhooks.svc.cluster.local
piggysec.com/aws-secret-name: demo/sample/test
piggysec.com/aws-region: ap-southeast-1
spec:
containers:
- image: ghcr.io/kongz/piggy-demo:latest
name: demo
env:
- name: TEST_ENV
value: piggy:TEST_ENV
resources:
limits:
memory: "64Mi"
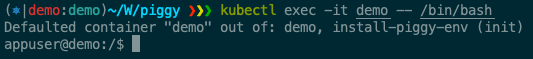
cpu: "200m"Use kubectl exec -it demo -- /bin/bash to execute into pod
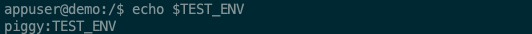
Just simply echo $TEST_ENV and see the result. The environment variable value is not resolved. You won't see the value on container shell.
> echo $TEST_ENV
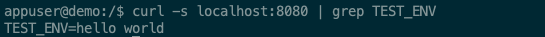
> piggy:TEST_ENVNow, try to curl to demo app and let's app resolve the environment variable
> curl -s localhost:8080 | grep TEST_ENV
> TEST_ENV=hello worldThe SSM Parameter Store has no additional charge for storage in standard throughput. It can store only up to 4096 characters and it can't replica to another region. But it is much cheaper than AWS Secret Manager.
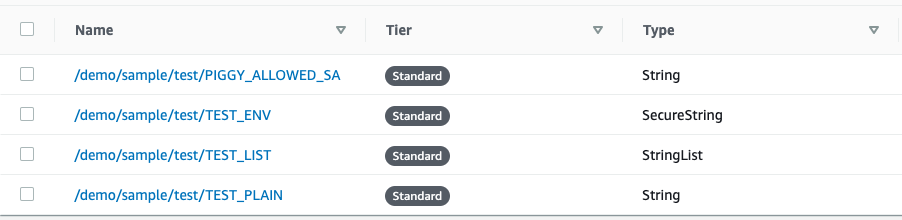
The demo here will retrieve the secret name TEST_ENV from AWS parameter store path /demo/sample/test/TEST_ENV, /demo/sample/test/TEST_LIST and /demo/sample/test/TEST_PLAIN
The simplest IRSA Policy for Piggy webhooks
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "piggySSM",
"Effect": "Allow",
"Action": [
"ssm:GetParametersByPath"
],
"Resource": "*"
},
{
"Sid": "PiggyECRReadOnly",
"Action": [
"ecr:BatchCheckLayerAvailability",
"ecr:BatchGetImage",
"ecr:DescribeImages",
"ecr:GetAuthorizationToken",
"ecr:GetDownloadUrlForLayer"
],
"Effect": "Allow",
"Resource": "*"
}
]
}Assume you are already install piggy-webhooks. If you are not install the piggy-webhooks yet, checkout steps from above.
Create a pod with annotations to piggy-webhooks service, ssm parameter path, and aws-region.
You can see a yaml file at demo/ssm/pod.yaml. The demo is also provide a service account in case if you enable PIGGY_ENFORCE_SERVICE_ACCOUNT
apiVersion: v1
kind: Pod
metadata:
name: demo
annotations:
piggysec.com/piggy-address: https://piggy-webhooks.piggy-webhooks.svc.cluster.local
piggysec.com/aws-ssm-parameter-path: demo/sample/test
piggysec.com/aws-region: ap-southeast-1
spec:
containers:
- image: ghcr.io/kongz/piggy-demo:latest
name: demo
env:
- name: TEST_ENV
value: piggy:TEST_ENV
- name: TEST_LIST
value: piggy:TEST_LIST
- name: TEST_PLAIN
value: piggy:TEST_PLAIN
resources:
limits:
memory: "64Mi"
cpu: "200m"Now, try to curl to demo app and let's app resolve the environment variable like the demo in AWS Secret Manager above
> curl -s localhost:8080 | grep TEST_ENV
> TEST_ENV=hello world