-
Notifications
You must be signed in to change notification settings - Fork 325
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Support Custom Protocols in WebExtension #164
Comments
|
Support for simplified redirect-based protocol handler (simple redirect, no origin support) landed in Firefox 54: This a a thin UX on top of
Note that this is just a redirect:This means the address in location bar changes (Origin barrier is broken) and there are different security context for public and local gateways (different cookies, etc). And yes, this is Firefox-only. |
|
It seems that this new API has the same naming limitation as Chrome, firefox-54.0a2 says:
This means we can't support |
|
When we get official registration of the schema we should be able to request the exemption to be added. |
- implements simplified handlers described in #164
|
I've just tested a ridiculous PoC that restores support for
Well.. it just works 🚀 🙃 (not sure if I am proud or ashamed, probably both) Expect PR in near future. My plan is to polish and ship this workaround as the default behavior, so that there is no functional regression when users update from v1.6.0 to v2.x.x. Of course there will be a preference that disables this: to pass review at Mozilla and in case someone really wants to search for Update 2017-12-27: this hack does not work on Android – see #348 |
This is an implementation of ridiculous idea from: #164 (comment) I am really sorry.
This is an implementation of ridiculous idea from: #164 (comment) I am really sorry.
|
FYSA some recent developments (Q3 2018):
|
|
If DWeb protocols get safelisted, we need Filled a Chrome bug: Extensions API should implement manifest.json/protocol_handlers. |
|
According to the URI syntax in RFC3986, it should not be "ipfs://{cidv1b32}", instead it should be "ipfs:{cidv1b32}". Same for {hash}. The extention should then use its default IPFS instance to retrieve the object {cidv1b32}. See https://tools.ietf.org/html/rfc3986#section-3 '//' denotes a specific instance. So an IPFS service on localhost could be addressed with "ipfs://localhost/{cidv1b32}", while IPFS running on ipfs.io would be "ipfs://ipfs.io/{cidv1b32}" |
|
Those are good points, thanks for raising them @ingokeck
|
|
5 years after Firefox, Google Chrome is now willing to implement the protocol_handler for registering custom handlers via web extensions: w3c/webextensions#317 (comment) |
|
Igalia is working on Chromium improvement to allow redirect-based handler registration with protocol_handlers in browser extension manifest. Completed the design document (The protocol_handlers Web Extension's Manifest key) with the permissions management and conflict resolutions, and shared the design document with Google for feedback. Assuming that eventually lands in Chromium-based browsers, the next step will be to allow using the API for pointing protocol scheme at Service Worker, instead of URL. This will allows for keeping This will take even more time, for now the idea is tracked in: |
(living summary: updated @ 2018-09)
This issue tracks browser extension support for various protocol schemes and URIs according to four stages of the upgrade path for path addressing and IPFS Addressing in Web Browsers memo, namely:
URLs:
URI:
This issue also tracks (currently nonexistent) ways to address/workaround how Origin is calculated (Problem #2)
WebExtension APIs
Universal API
No such thing yet (but see WIP work in comments)
Firefox
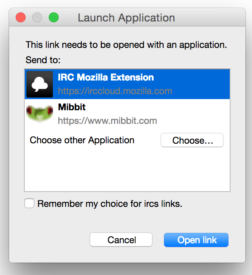
web+fsprotocol is supported as a redirect: Support Custom Protocols in WebExtension #164 (comment)web+prefixipfs://in address bar.It can be found in
libdwebbranch. More info in PR [PoC] libdweb experiment: protocol handler API #533 and /libdweb/docs/libdweb.mdChrome / Chromium
web+prefix for non-safelisted protocolsweb+prefix (context: Safelisting DWeb Protocols arewedistributedyet/arewedistributedyet#23)Brave
Muon-based (deprecated in 2018)
browser.protocol.registerStringProtocolavailable to trusted extensionsChromium-based
Related discussions
The text was updated successfully, but these errors were encountered: